News

Raz-Lee at COMMON POWERUp 2026 in New Orleans
The Raz-Lee team was proud to participate in COMMON POWERUp 2026, one of the largest and most important gatherings for the IBM i community. Held in vibrant New Orleans, the event brought together IBM i professionals, technology
Next Generation Release News of iSecurity. April 2026
Next Generation Release News of iSecurity. April 2026 Changes in virtually all iSecurity products More inter product synergy Available with subscription iSecurity Suite (*BASE) License file is intended to support organization with multiple licenses. Licenses for
Next Generation Release News of iSecurity Base Program New Features
iSecurity Suite (*BASE) The iSecurity Base component delivers centralized license management, operational resilience, and enhanced system visibility across IBM i environments. Centralized License Management A single license file supports multiple products across one or multiple LPARs. Automatically
Micro-Segmentation Advantages with iSecurity Firewall on IBM i
Modern IBM i environments are no longer isolated systems. They are connected to web applications, APIs, cloud services, remote users, and third-party integrations. In this reality, perimeter security is not enough. Micro-segmentation becomes a critical control. iSecurity
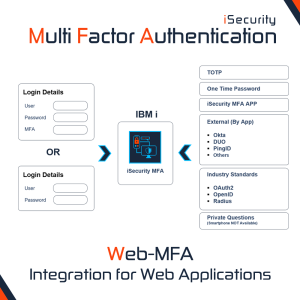
New Feature: Web-MFA Integration for Web Applications
Raz-Lee Security introduces Web-MFA, a powerful new enhancement to iSecurity Multi-Factor Authentication (MFA), designed to extend strong authentication beyond IBM i and into your web applications. Integration with Ease With Web-MFA, organizations can seamlessly integrate their websites
Why to implement an EDR framework on IBM i?
The IBM i platform often serves as a cornerstone for business-critical operations: ERP, financials, manufacturing, healthcare systems. It stores highly sensitive data, configuration objects and system values whose integrity is essential … they store … sensitive assets
